Call Spoofing Scam Surge In Australia.

Call Spoofing Scam Surge In Australia.
Australia: There is a surge in call spoofing scams in Australia. These calls that are received show that the call is from the reputed company to from their known numbers. These calls are termed call spoofing.
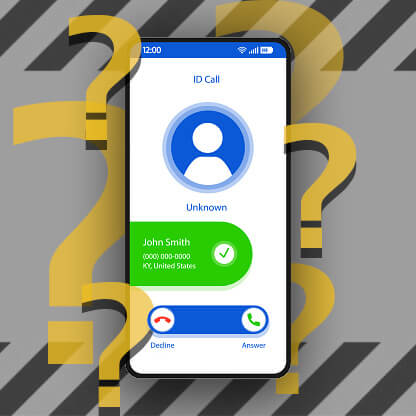
Telstra the telecommunication agency of Australia has stated that call spoofing has increased in-country from the past few months. This is called the latest tool or weapon used by cyber thugs or criminals to do the crime. These attack surges because they make it easy for the criminals to make the victim attend the call.

Pandemic lets this increase because Australians were spending more time on their phones and were spending more time for having the communication from the officials of their service provider.
These cybercriminals work smartly as they know that it is difficult for them to make victims attend unknown calls or calls from another country for work purposes. So they spoof the call before calling the victim. Which shows that the call comes from the legit person or from the legit agency.
This is a kind of social engineering technique used by cybercriminals in order to gain the trust of the victim and then perform what they want to do. Some call spoofing call connects you to the person who extracts money from the victim falsely. In many cases, they warn the victim and even also gave them threats like they gonna lose all the money if they won’t be able to pay the money.
They may also do spoofing in order to extract he or gather the information from the victim in order to gain access to other things.
They are also sending SMS through spoof numbers stated that they have voicemails and can be listened to after downloading the app whose link was given in the SMS. And that link was from the malicious app ‘Flubot’.

Warning: Do not install such apps on your mobile phone ( ANDROID/IOS). Because it can easily give access to all the stuff which is present in your mobile phone.