Man In The Middle (MITM)
Man In The Middle Attack (MITM)
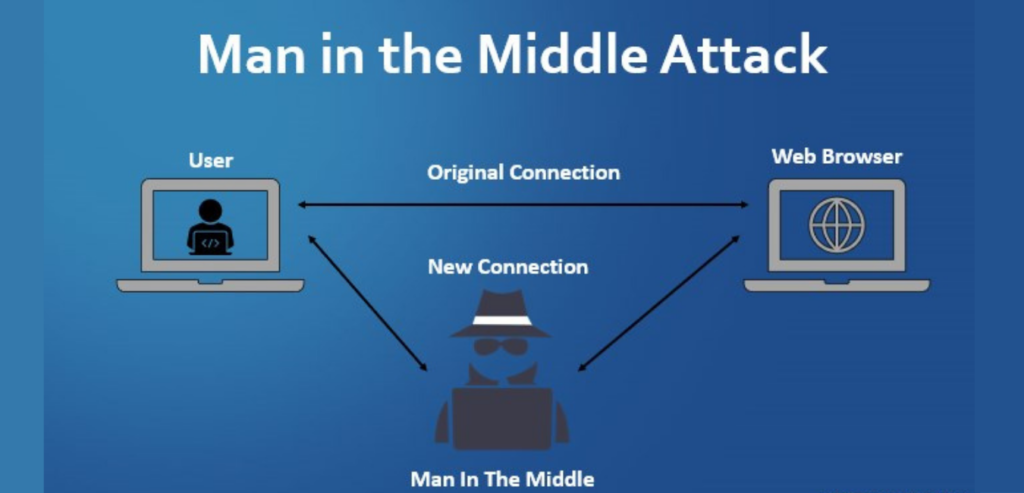
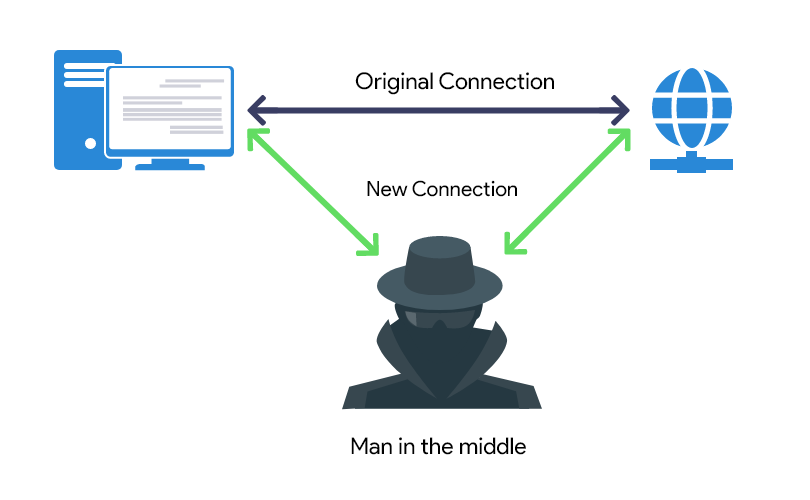
In this section, we will discuss man-in-the-middle (MITM) attacks. This is one of the most dangerous attacks performed on the network. We perform this attack after connecting to the network. This attack redirects the flow of packets from any client to our device. This means that any data packets sent to or from the client must pass through our device. Now that we know the password and key of the network, we will be able to read only these packets, modify them, and discard them. This kind of attack is so effective and powerful because it is difficult to prevent. This is due to the way the ARP protocol works.
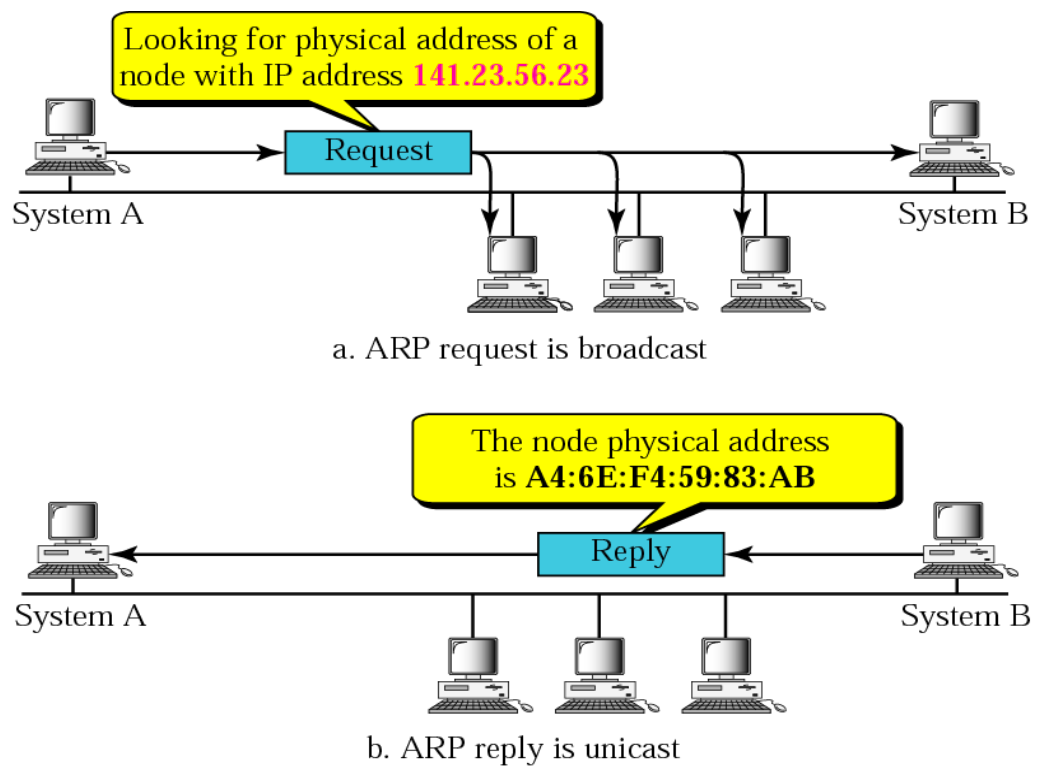
ARP has two main security issues. The first security issue is that every ARP request and response is trustworthy, so whatever our device says to other devices in the network is trustworthy. If we tell us that any device on the network is a router, the device will trust us. It will not run any tests to make sure that we are not routers. Likewise, if we tell the router that we are someone else on the network, the router will trust us and will begin to treat us as the device. This is the first security issue. The second security issue is that the client can accept a response even if it has not sent a request. Therefore, when a device is connected to a network, the first thing to ask is, who is the router? Then the router will send a reply saying “I am the router”. Now, we can send a response without the device asking who the router is. We can tell the device that we are a router, and because the device trusts anyone, they will trust us and start sending data packets to us instead of sending them to the real router.
Next, we will understand how MITM attacks work. It will use a technique called ARP poisoning or ARP spoofing. In the picture below, we can see a typical Wi-Fi network. When the client requests something, it will send the request to the Wi-Fi router, and then the router will get the request from the Internet and return the response to the client:
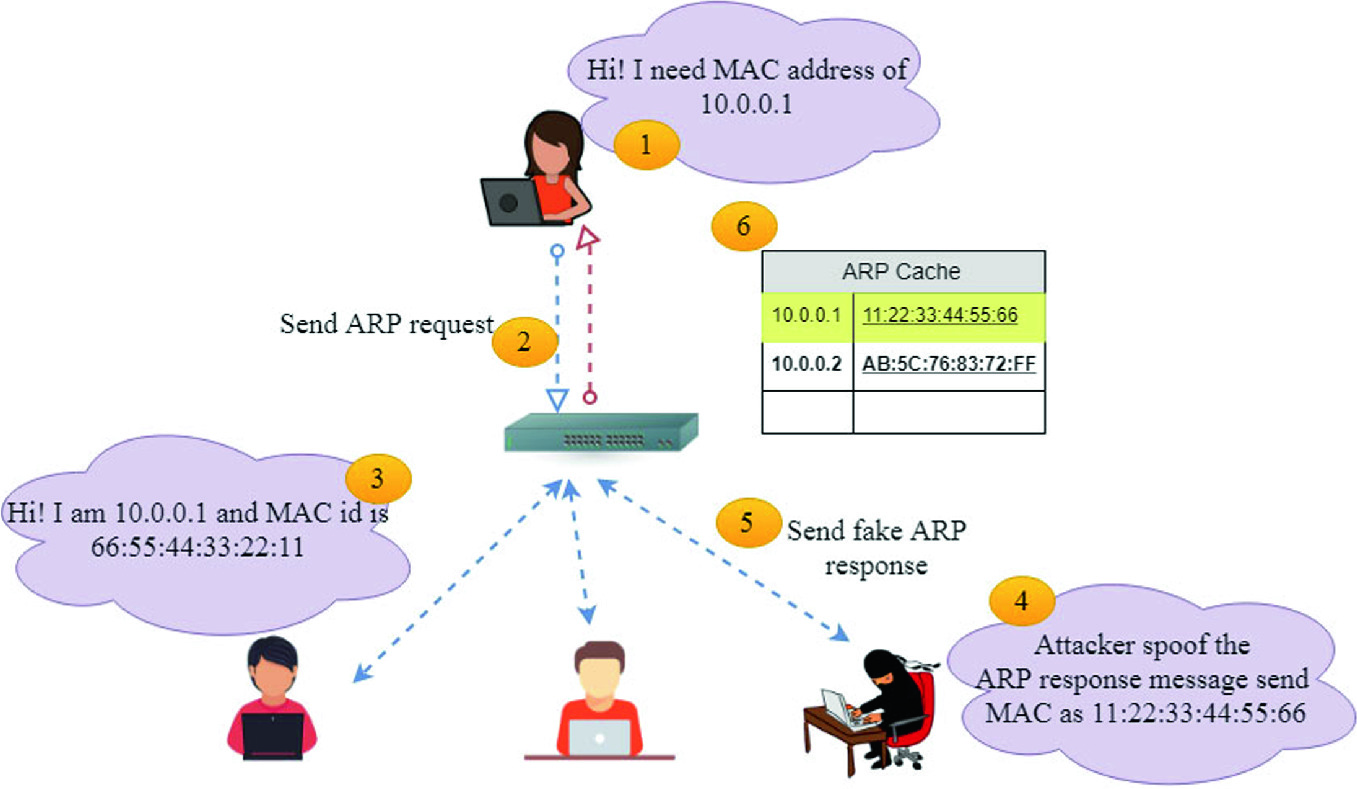
All of this is done using data packets. Therefore, what we have to do is to send an ARP response to the client so that the response can be sent without the client asking again. The client did not ask for anything, but we can still send a reply. We want to say that our IP is the router IP. IP routers 10.0.0.1 are: . We have to tell the client that the IP 10.0.0.1 device has our MAC address, so we have to tell the client that we are a router.
After that, we will do the opposite with the Wi-Fi router. We want to tell the router that we are the client. We Will do this by telling the router that our IP is the client IP, and the client has our MAC address, so the communication of the data packet will be done through the MAC address, and the Wi-Fi router will start sending us the data packet- This turned out to be a packet to be sent to the client.
So, this is the basic principle of ARP poisoning or MITM attack. The principle of the attack is: we will tell the client that we are a router, and then we will tell the Wi-Fi router that we are a client. This will put us in the middle of the packet flow between the client and the Wi-Fi router. After this, all data packets will start to flow through our device, so we can read data packets, modify data packets or delete data packets.