foot Printing

Footprinting
Footprinting is a method that’s used by hackers to collect information about their victim such as victim network, computer system, devices, ETC. footprinting the first phases of ethical hacking. And this the most important phase for hackers. By footprinting, attackers try to gather all available information about their victims in order to get unauthorized access to a victim network or computer system.
Objectives of foot-printing
Know Security posture: Analyse the security posture of the target, find loopholes, and create an attack plan.
Identify focus area: Using different tools and techniques, narrow down the range of IP addresses.
Find vulnerabilities: use the collected information to identify weaknesses in the target’s security
Map the network: Graphically represent the target’s network and use it as a guide during the attack.
Types of foot-printing
There are two types of footprinting
- Passive footprinting
- Active footprinting
Passive foot-printing:
- Collecting information without interacting with the target directly.
- Through search engines or public records.
- Used when information gathering must not be detected by the target.
Active foot-printing
- Collecting information by interacting with the target directly
- There is a chance that the target becomes aware of the information gathering.
- Info more accurate and rapid
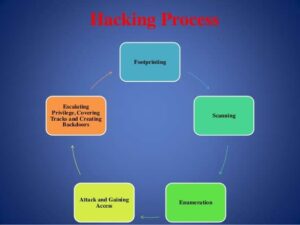
Footprinting Methodology
- Website footprinting
- Email footprinting
- Footprinting using google
- DNS footprinting
- Network footprinting
- Footprinting through Social Engineering
- Footprinting Through Social Networking Sites
- Footprinting Through Search Engines
- WHOIS Footprinting
Some Tools and websites that you can use for Footprinting.
- Whois Lookup
- Nslookup
- What web
- Wappalyzer
- DNS Dumpster
- Harvester
- OSINT Framework
- Netcraft
- Nmap
- Maltego
- Shodan
- Nikto